If your company processes, stores, or transmits cardholder data and you have not yet fully migrated to PCI DSS 4.0, you are operating outside compliance today. There is no more waiting period. The standard became fully mandatory in March 2025, and as of 2026, payment brands are enforcing it. This blog breaks down what PCI DSS 4.0 requires, what it costs to ignore it, and how fintech founders and entrepreneurs can build compliance into their payment infrastructure from the ground up, bolt it on after a failed audit.

What actually changed with version 4.0
PCI DSS 3.2.1 was retired in March 2024. Version 4.0 introduced 64 new or updated requirements in total 13 took effect immediately upon adoption, and the remaining 51 became mandatory in March 2025. The two biggest conceptual shifts are ones every founder should understand before any technical detail:
From point Intime to continuous.
Under 3.2.1, you passed an annual audit and were considered compliant until the next one. Version 4.0 treats compliance as an ongoing security posture, not a snapshot. Your controls must work every day, not just on audit day.
From rigid prescription to objective based flexibility.
4.0 introduced the Customized Approach, which lets you achieve security objectives using methods appropriate for your architecture including AI driven monitoring, modern cloud native controls, and automated tooling. The trade-off is that custom approaches require more documentation and a targeted risk assessment for each deviation.
The practical meaning for startups: You cannot buy compliance from a checkbox vendor once a year. Your systems, your access controls, and your monitoring need to work continuously and you need to be able to prove it.
The three requirements that hit scaling startups hardest
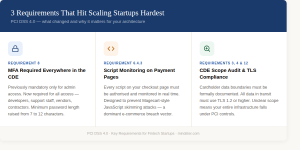
1.MFA is nowrequiredeverywhere in the CDE, not just for admins
Previously, multifactor authentication was only mandatory for administrator level access to the Cardholder Data Environment (CDE). Under 4.0, MFA is required for all access including developers, support staff, and any vendor or contractor who can reach cardholder data. If you use shared credentials, reuse passwords, or allow single factor access to any CDE system, you are noncompliant today.
Password minimums also increased. 4.0 requires a minimum of 12 characters for all CDE accounts.
2.Script monitoring on payment pages
Mage cart style attacks where malicious JavaScript is injected into checkout pages to silently skim card data became one of the dominant breach vectors in ecommerce. Version 4.0 responds directly: you must deploy automated tools to manage and authorize every script running on your payment pages. Any unauthorized script must be detected and blocked in real time. For startups using third party payment widgets or CDN loaded libraries, this is a nontrivial implementation requirement.
3.Scope creep in your CDE
As startups grow rapidly, cardholder data tends to spread. A database that starts containing only tokenized data ends up with raw PAN data because someone added a field “temporarily.” A development environment that was never meant to hold real card numbers does. Version 4.0 requires a rigorous audit of your CDE boundaries, documented scope definitions, and TLS 1.2 or higher for all data in transit. If your scope is unclear, your entire infrastructure becomes subject to PCI controls an enormous compliance and operational burden.
What noncompliance actually costs
Noncompliance penalties are imposed by payment card brands through your acquiring bank, triggered by a breach or a failed audit. Once imposed, they escalate the longer you remain out of compliance.

For startups specifically: Losing your merchant account the ability to process card payments is effectively a business shutdown. Card brands can revoke processing rights for sustained noncompliance. This is not a theoretical risk.
On the other side: if a breach occurs but you are found to be fully PCI DSS compliant, card brands have discretion to reduce or eliminate fines. Compliance is your protection as much as it is a regulatory obligation.
What leadership needs to own
PCI DSS 4.0 explicitly requires that compliance have leadership visibility not just an assignment to a security team. Version 4.0 mandates documented roles and responsibilities for all 12 requirement domains, and auditors will look for evidence that executives are informed of the organization’s security posture on a regular basis.
In practical terms, this means two things for founders and CEOs:
Formally assign ownership of each PCI requirement domain to named individuals. “The security team” is not an acceptable assignment. Requirements must map to specific roles.
Establish a compliance review cadence quarterly at minimum where security posture, open gaps, and remediation timelines are presented to leadership. Auditors treat this as evidence of governance, not just good practice.
Update internal security policies to reflect the continuous compliance model. If your policy still describes annual reviews, it is out of alignment with 4.0’s requirements.
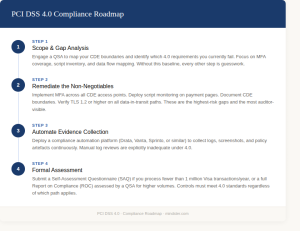
A realistic 2026 roadmap
If your organization has not completed migration, here is a sequenced approach. The order matters scope definition and gap analysis must come first, because remediating the wrong systems wastes both time and budget.
The business case for getting this right
Compliance is not only a cost centre. For fintech startups, a clean PCI DSS 4.0 posture directly affects growth in three ways:
Enterprise sales
Compliance reduces deal friction
Enterprise procurement and security due diligence routinely requires evidence of PCI compliance before a contract is signed. A current Report on Compliance or SAQ shortens security reviews from months to days. For startups trying to close large contracts, this is not a nice-to-have.
Market expansion
New payment methods and markets require compliance as a prerequisite
Adding buy now pay later, digital wallets, or entering regulated markets in the EU or Southeast Asia all build on your existing PCI compliance foundation. Organizations with documented, modular compliance frameworks expand faster because they do not need to rebuild security controls from scratch for each new product.
Customer trust
88% of customers won’t transact with companies they don’t trust
A publicized breach in financial services is not a recoverable event for most startups. The cost of customer acquisition in fintech is too high, and trust, once lost in payments, is rarely rebuilt. Compliance is the floor not the ceiling of what customers expect.
How Mindster helps fintech companies build for compliance from the ground up
Most compliance gaps in scaling fintechs are not policy failures they are engineering failures. Insecure architectures, untracked data flows, poorly scoped CDEs, and bolted on authentication are built-in problems that a compliance checklist cannot fix after the fact. Mindster is a product engineering firm that works with fintech companies specifically to build secure, compliant infrastructure before it becomes a liability.
Here is where their capabilities map directly to PCI DSS 4.0 requirements:
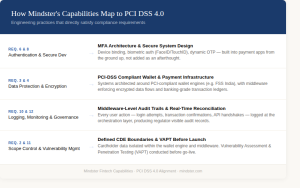
Requirement 6 & 8 Authentication & Secure Development
MFA architecture and secure system design
Mindster builds multifactor authentication into the core of payment applications not as a layer added later. Their fintech projects use device binding, biometric authorization (FaceID/TouchID), and dynamic OTP flows, which directly satisfy PCI 4.0’s requirement for MFA across all CDE access points and nonrepudiation of transactions.
Requirement 3 & 4 Data Protection & Encryption
PCIDSS compliant wallet and payment infrastructure
Their payment systems are architected around PCIDSS compliant wallet engines (such as FSS India), with middleware layers that enforce encrypted data flows and banking grade transaction ledgers. In their ONEIC project, this architecture produced a complete, regulator visible audit trail across every transaction lifecycle the kind of evidence trail QSAs look for during a 4.0 assessment.
Requirement 10 & 12 Logging, Monitoring & Governance
Middleware level audit trails and real-time reconciliation
PCI 4.0 requires automated log reviews and continuous monitoring. Mindster’s middleware architecture captures every user action login attempts, transaction confirmations, API handshakes at the orchestration layer. This produces the immutable audit trail regulators and QSAs require, without relying on manual log reviews.
Requirement 2 & 11 Scope Control & Vulnerability Management
Defined CDE boundaries and security tested systems
Mindster conducts Vulnerability Assessment and Penetration Testing (VAPT) before launch and builds systems with clearly scoped data boundaries keeping cardholder data isolated within the wallet engine and middleware, away from other application layers. This directly addresses the scope creep problem that gets scaling startups flagged in audits.
Mindster in practice: building a PCI compliant payment system at national scale
ONEIC National Scale Digital Wallet for Oman’s Largest Payment Provider
ONEIC (Oman National Engineering & Investment Co.) is the largest licensed Non Banking Financial Institution and payment service provider in Oman. They needed to transition from a traditional billing operation to a fully licensed digital wallet provider integrated with the Central Bank of Oman’s national payment switch (MPCSS) while meeting strict PCIDSS standards.
Mindster built the end-to-end infrastructure: a PHP Laravel middleware layer that acted as the financial brain of the system, a Flutter based mobile app, and direct integration with the FSS PCIDSS compliant wallet engine. Security was built in biometric MFA, device binding, dynamic OTP, a 24hour cooling off period for new accounts, and automated KYC through Uqudo’s biometric identity verification.

The result: 500,000+ active users onboarded within 12 months, 80% reduction in manual processing, 100% success rate in preventing unauthorized account takeovers, and full regulatory compliance with Central Bank mandates maintained continuously, not just at audit time.
If you are building or scaling a payment product and compliance is a current or upcoming pressure point, Mindster’s fintech team can be reached at mindster.com/contactus.
If you are not compliant yet, act immediately
Noncompliance does not go unnoticed indefinitely. Fines are triggered when a breach occurs or when an audit flags gaps and once triggered, they escalate every month you remain out of compliance. The longer the gap between where you are and where 4.0 requires you to be, the worse the outcome when that moment arrives. The following actions have no reasonable delay:
Map your CDE today. Run an internal audit of every system that touches cardholder data what stores it, transmits it, or processes it. Until you know your actual scope, you cannot fix anything accurately.
Lock down CDE access immediately. Verify MFA is active for every user and vendor with CDE access not just administrators. If it is not, that is a live compliance violation, not a pending one.
Audit your payment page scripts now. If you cannot immediately list every authorized script running on your checkout pages and its purpose, that gap exists in production right now.
Engage a QSA without waiting for your next audit cycle. If your compliance status is unclear, an independent assessor will tell you exactly where you stand and what exposure you are carrying. That conversation should happen before your next board meeting.
Assign named owners for each requirement domain. “The security team” is not an assignment. PCI 4.0 auditors look for specific individuals accountable for specific controls. If those names do not exist, create the structure before anything else.
If you are already compliant, the priority shifts to maintaining that posture continuously not just at audit time. Version 4.0 treats a lapse between audits the same as noncompliance. Set automated monitoring, not calendar reminders.
FAQ
1.Does PCI DSS 4.0 apply to my startup if we use Stripe or a third-party payment processor?
Yes, but your scope may be significantly reduced. If you use a fully hosted payment page where the card form is served entirely by Stripe or your processor and card data never touches your servers you likely qualify for SAQ A, the simplest self-assessment. However, you are still required to complete an annual SAQ and document an Attestation of Compliance. Outsourcing payment processing does not remove your PCI obligations. You remain responsible for the security of your integration, your checkout page, and any third-party scripts on that page.
2.What is the difference between SAQ A, SAQ A-EP, and SAQ D and which one applies to me?
The SAQ type depends entirely on how your payment flow is built. SAQ A applies if your payment page is fully hosted by a compliant third party and card data never touches your environment. SAQ A-EP applies if you have your own payment page with JavaScript that redirects to a processor this requires script monitoring and integrity checks under Requirement 6.4.3. SAQ D is the most comprehensive and applies to merchants who store, process, or transmit cardholder data directly. Getting your SAQ type wrong determines which controls you need to implement and that mistake is common and costly.
3.How long does it take to become PCI DSS 4.0 compliant?
It depends almost entirely on your architecture and how well your CDE is scoped. Startups with clean, segmented designs can reach compliance in 8–12 weeks. Companies with broader scope where card data touches multiple systems or legacy infrastructure is involved can take 6–9 months. The single biggest driver of timeline and cost is scope size. Early decisions around tokenisation and network segmentation have the highest leverage on how fast and cheaply you can get there.
4.What is the Customized Approach in PCI DSS4.0and should my startup use it?
The Customized Approach lets you meet a security objective using methods of your own design rather than following the exact prescribed control. For example, instead of a specific log review tool, you could use AI-driven anomaly detection that meets the same objective. The tradeoff is documentation every customised control requires a Targeted Risk Analysis validated by a QSA. For most early-stage startups, the standard defined approach is simpler and cheaper. The Customized Approach is most valuable for mature companies that have already outgrown prescriptive controls.
5.Does tokenisation make us PCI DSS compliant?
No and this is one of the most persistent misconceptions. Tokenisation reduces your scope by replacing card numbers with tokens, but poorly implemented tokenisation can still leave systems in scope. If raw card data touches your servers even briefly before being tokenised, those systems are in scope. If your tokenisation solution is not itself validated as PCI-compliant, you may carry more liability than you realise. Tokenisation is a scope-reduction tool, not a compliance substitute.
6.What happens if a breach occurs and we are not PCI DSS compliant?
The consequences compound. Card brands can impose fines from $5,000 to $100,000 per month, retroactive to when non-compliance began. You may also be liable for forensic investigation costs, card reissuance for affected customers, and legal fees all typically passed through your acquiring bank. In serious cases, your merchant account can be revoked, which means you lose the ability to process card payments entirely. On the other side: if a breach occurs and you are found fully compliant at the time, card brands have discretion to significantly reduce or waive fines. Compliance is your primary legal protection in a breach scenario.
7.Is PCI DSS 4.0 compliance a one-time project or an ongoing requirement?
Ongoing — and this is the fundamental shift in version 4.0. Under the previous standard, passing an annual audit was effectively sufficient. Version 4.0 requires continuous controls, real-time monitoring, and documented evidence that those controls are working throughout the year — not just at audit time. Security awareness training must be reviewed annually, risk assessments must be performed whenever significant changes occur, and CDE scope must be reviewed at least annually (every six months for service providers). Treating compliance as a project with a finish line is the most common reason companies fail their next audit.
8.We use AWS, GCP, orAzure doesthat cover our PCI DSS obligations?
Partially. Major cloud providers hold PCI DSS Level 1 service provider certification, which covers the infrastructure they manage. But cloud compliance works on a shared responsibility model the provider secures the underlying infrastructure; you are responsible for everything on top of it. Your application code, access controls, storage configuration, encryption key management, and monitoring are your responsibility regardless of which cloud you use. Running on a compliant cloud does not transfer compliance to you.
9.What does PCI DSS 4.0 require for APIs?
APIs are now explicit audit targets under version 4.0. They must be included in your software inventory under Requirement 6.3.2, authenticated with strong controls, rate-limited against abuse, and logged at the detail level required for audit trails. If your payment platform is API-first which describes most modern fintechs your entire API security posture is in scope and will be assessed. This covers both internal APIs between microservices and external APIs exposed to partners or customers.

Professional content writer Akhila Mathai has over four years of experience. She writes posts about the different mobile app solutions we offer as well as services related to them. Her ability to conduct thorough research and think critically enables her to produce excellent, authentic, and legitimate content. Along with her strong communication abilities, she collaborates well with her teammates to create information that is current and relevant to emerging technology.